In the contemporary digital landscape, the journey of a photograph from a creator’s camera to a global audience is fraught with technical hurdles that often sever the link between the artist and their work. This phenomenon, known as the loss of provenance, describes the disappearance of the chronological record or trail of ownership and origin of a digital asset. For professional photographers and hobbyists alike, the scenario is increasingly common: a high-quality image is captured, shared, and subsequently goes viral across social media platforms, yet the original creator receives neither credit nor compensation because the identifying information has been systematically erased. While the industry has attempted to address this through various technical standards, a significant gap remains between the creation of content and its distribution through major tech intermediaries.
The Evolution of Digital Content Authentication
The concept of provenance is not new to the art world, where it has long served as a vital tool for verifying the authenticity and history of physical masterpieces. In the digital realm, however, the challenge is compounded by the ease with which files can be copied, edited, and redistributed. For years, photographers relied on EXIF (Exchangeable Image File Format) and IPTC metadata to embed their names, copyright notices, and location data into their image files. However, this metadata is easily stripped by even the most basic photo editing software or social media upload algorithms.
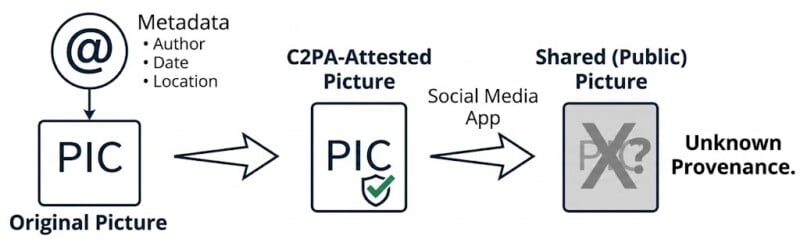
To combat this, the Coalition for Content Provenance and Authenticity (C2PA) was formed. This industry-wide effort represents a collaborative venture between tech giants including Adobe, Microsoft, Google, Amazon, and Meta, alongside hardware manufacturers like Sony, Nikon, and Leica. The C2PA standard aims to create a tamper-evident record of an image’s journey. By capturing specific details at the moment of the shutter press—such as the author, timestamp, and GPS coordinates—and cryptographically "binding" them to the file, C2PA was designed to ensure that wherever an image travels, its pedigree follows.
Despite the backing of the world’s most powerful technology companies, the adoption of C2PA remains remarkably low. A 2024 report from the Reuters Institute for the Study of Journalism highlighted a sobering statistic: currently, fewer than 1% of news images or videos published globally include C2PA provenance information. This slow integration suggests that while the technology exists, the infrastructure of the internet is not yet optimized to preserve it.
The Social Media Bottleneck and the "Bouncer" Effect
The primary obstacle to the success of C2PA and similar metadata-based standards is the gatekeeping role of social media platforms. When a photographer uploads an image to platforms like Instagram, X (formerly Twitter), or TikTok, the file undergoes an automated processing phase. During this stage, platforms prioritize load speeds and bandwidth conservation. Consequently, images are heavily compressed, and nearly all non-essential metadata is stripped away.
Industry experts often compare these platforms to a "bouncer" at a high-security club. Just as a bouncer might confiscate a patron’s identification at the door, social media algorithms remove the digital ID of an image before allowing it to enter the public feed. While the metadata component of a standard JPG or PNG file is relatively small—averaging approximately 100kB—the cumulative impact of this data on a global scale is staggering.
According to data from Infosys and various digital trend reports, an estimated 14 billion images are uploaded to social platforms every single day. If every one of these images were to retain 100kB of C2PA metadata, tech companies would be required to accommodate an additional 1.4 petabytes of storage daily. Over a year, this would amount to over 500 petabytes of extra data. For companies operating on razor-thin margins of efficiency, the incentive to preserve this information is outweighed by the massive infrastructure costs associated with storage and the increased bandwidth required to serve "heavier" files to mobile users.
The Incentives Gap and Institutional Inertia
The lack of progress in provenance preservation can also be attributed to a misalignment of incentives. For the photographer, the incentive is clear: professional recognition, copyright protection, and potential monetization. However, for the social media platforms, the incentives are less obvious. Preserving provenance does not inherently drive user engagement or increase ad revenue. In fact, it adds technical complexity and cost.
Furthermore, there is a lack of public pressure. While the photography community is vocal about attribution, the general public rarely demands to see the metadata of a viral meme or a landscape photo in their feed. This has led to a situation where tech companies can signal their support for C2PA in press releases and industry white papers—maintaining a positive reputation within the creative community—while doing very little to implement the standard in their core consumer-facing products.
Perceptual Hashing: A New Frontier in Image Identification
As C2PA struggles with adoption and platform compatibility, a different technology known as perceptual hashing (pHash) is gaining traction as a more resilient alternative. Unlike traditional metadata, which is "attached" to a file, pHash creates a unique digital fingerprint based on the visual content of the image itself.
A pHash algorithm analyzes the structural patterns, colors, and gradients of an image to produce a string of characters (often 64 characters long). This string acts as a "fingerprint." The revolutionary aspect of pHash is its durability; because the fingerprint is derived from the visual information, it remains largely consistent even if the image is cropped, compressed, or resized.

The workflow for a pHash-based system differs significantly from metadata standards:
- Creation: A photographer generates a pHash for their original work and registers it in a database.
- Distribution: The image is shared, stripped of metadata by social media, and goes viral.
- Verification: A user or an automated system encounters the image and runs it through a pHash tool. The tool generates a fingerprint for the "found" image and compares it against the database.
- Match: Because the visual structures match, the system identifies the original creator, regardless of the lack of embedded metadata.
This "Shazam-for-images" approach bypasses the need for cooperation from social media platforms. It does not require the platforms to store extra data or change their compression algorithms. Instead, the image itself serves as the key to its own history.
Comparative Analysis: Metadata vs. Fingerprinting
The debate between C2PA (metadata) and pHash (fingerprinting) is not a zero-sum game, but rather a discussion of utility and environment. C2PA is superior for "chain of custody" and professional journalism, where proving that an image has not been manipulated by AI or malicious actors is paramount. It provides a forensic trail that is essential for legal and historical record-keeping.
Conversely, pHash is arguably more effective for the "wild west" of the social internet. It solves the attribution problem for creators whose work is frequently reshared without consent. By shifting the burden of identification from the file’s "tags" to the file’s "appearance," pHash offers a level of permanence that metadata cannot match.
Broader Implications for AI and the Future of Media
The urgency of solving the provenance problem has been accelerated by the rise of generative Artificial Intelligence (AI). As AI-generated images become indistinguishable from real photography, the ability to verify the origin of a file has moved from a professional courtesy to a societal necessity.
If provenance standards are not successfully integrated, the "dead internet theory"—the idea that the majority of web content is bot-generated and artificial—becomes a closer reality. Establishing who created an image and whether it was captured by a human lens or synthesized by a prompt is critical for maintaining trust in digital media.
In the legal sphere, the outcome of this technological tug-of-war will likely influence future copyright legislation. If tools like pHash become ubiquitous, the "I didn’t know who the owner was" defense for copyright infringement will become obsolete. Courts may eventually require platforms to implement automated pHash scanning to ensure creators are credited or compensated when their work is utilized for commercial purposes or AI training sets.
Strategic Recommendations for Creators
In the current transitional period, photographers are encouraged to adopt a multi-layered approach to protecting their work. While waiting for social media platforms to adopt C2PA standards, creators can:
- Enable C2PA at the Source: Use cameras and software that support C2PA to ensure a professional-grade record exists for high-value assets.
- Utilize Hashing Services: Register work with emerging pHash-based platforms to ensure that even "stripped" versions of their images can be traced back to them.
- Advocate for Transparency: Support initiatives that pressure social media companies to respect content credentials and provide "attribution badges" for verified content.
The path forward for digital provenance will likely involve a hybrid of these technologies. While the "bouncer" at the social media club may still strip away the IDs of the images that enter, the development of visual fingerprinting ensures that the creator’s identity is woven into the very fabric of the image, making it impossible to truly disappear. The goal remains clear: in an era of infinite digital replication, the creator must remain inseparable from the creation.